俄罗斯如何做成美国历史上最大选举入侵 [美国媒体]
在今年四月一个下午的早些时候,俄罗斯总统弗拉基米尔 普京在圣彼得堡召开了包括大约400名记者,博主以及媒体高管的聚会。普京身着整洁的海军套装,在回答与会者问题时,他神态轻松甚至很自在。
How Russia Pulled Off the Biggest Election Hack in U.S. History
俄罗斯如何做成美国历史上最大选举入侵
On an April afternoon earlier this year, Russian president Vladimir Putin headlined a gathering of some four hundred journalists, bloggers, and media executives in St. Petersburg. Dressed in a sleek navy suit, Putin looked relaxed, even comfortable, as he took questions. About an hour into the forum, a young blogger in a navy zip sweater took the microphone and asked Putin what he thought of the "so-called Panama Papers."
在今年四月一个下午的早些时候,俄罗斯总统弗拉基米尔 普京在圣彼得堡召开了包括大约400名记者,博主以及媒体高管的聚会。普京身着整洁的海军套装,在回答与会者问题时,他神态轻松甚至很自在。
The blogger was referring to a cache of more than eleven million computer files that had been stolen from Mossack Fonseca, a Panamanian law firm. The leak was the largest in history, involving 2.6 terabytes of data, enough to fill more than five hundred DVDs. On April 3, four days before the St. Petersburg forum, a group of international news outlets published the first in a series of stories based on the leak, which had taken them more than a year to investigate. The series revealed corruption on a massive scale: Mossack Fonseca's legal maneuverings had been used to hide billions of dollars. A central theme of the group's reporting was the matryoshka doll of secret shell companies and proxies, worth a reported $2 billion, that belonged to Putin's inner circle and were presumed to shelter some of the Russian president's vast personal wealth.
有博主提及从巴拿马莫萨克 冯赛克(Mossack Fonseca)律师事务所被偷窃的超过一百万份文件,这是历史上最大规模的泄密,数据量达到2.6T,足足需要500张DVD光盘才能装满。在4月3日,也就是圣彼得堡论坛的四天之前,一个国际新闻集团,通过超过一年的调查,发布了给予此次泄密事件的第一份报道。这个报道系列揭露出一个大规模的腐败:Mossack Fonseca律师事务所通过法律操作隐藏了数十亿美金。整个报道的核心内容便是,普京的内部圈子通过像俄罗斯套娃一样的各种秘密的空壳公司和代理据报告隐藏了20亿美金,其中也包括俄罗斯总统的个人巨量财富。
When Putin heard the blogger's question, his face lit up with a familiar smirk. He nodded slowly and confidently before reciting a litany of humiliations that the United States had inflicted on Russia. Putin reminded his audience about the sidelining of Russia during the 1998 war in Kosovo and what he saw as American meddling in Ukraine more recently. Returning to the Panama Papers, Putin cited WikiLeaks to insist that "officials and state agencies in the United States are behind all this." The Americans' aim, he said, was to weaken Russia from within: "to spread distrust for the ruling authorities and the bodies of power within society."
听到这个博主的问题,普京脸上露出熟悉的迷之微笑。普京慢慢地,自信地点头,然后历数美国加在俄罗斯身上地种种陈词滥调式的羞辱,接着普京又向观众提及1998年科索沃战争俄罗斯的边缘地位以及最近美国干涉乌克兰的所见所闻。然后又将话题转回巴拿马文件,普京引述维基解密强调“美国官员与政府机构才是这一切事件的幕后黑手”,他接着说,“美国这样做是为了在社会内部散步对执政当局和权力机构的不信任感,从而从内部削弱俄罗斯“
Though a narrow interpretation of Putin's accusation was defensible—as WikiLeaks had pointed out, one of the members of the Panama Papers consortium had received financial support from USAID, a federal agency—his swaggering assurance about America's activities has a more plausible explanation: Putin's own government had been preparing a vast, covert, and unprecedented campaign of political sabotage against the United States and its allies for more than a year.
尽管普京对美国的控诉这一有限的解释有一定的辩护力,就像维基解密所指出的那样,巴拿马文件事件调查团的一个成员接受了美国国际开发署的资金援助,但是对普京言之凿凿时美国主导了这一切有一个更加看似合理的解释:普京当局为美国及其盟友准备了一场巨大的,秘密的,空前的政治破坏活动,这项准备时间已超过一年。
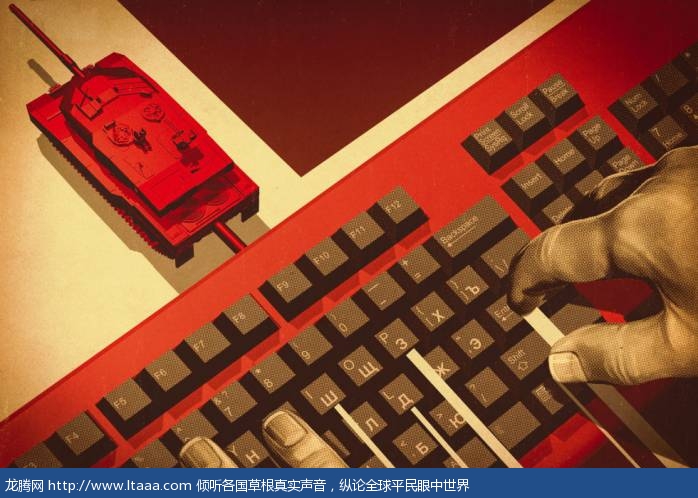
The Russian campaign burst into public view only this past June, when The Washington Post reported that "Russian government hackers" had penetrated the servers of the Democratic National Committee. The hackers, hiding behind ominous aliases like Guccifer 2.0 and DC Leaks, claimed their first victim in July, in the person of Debbie Wasserman Schultz, the DNC chair, whose private emails were published by WikiLeaks in the days leading up to the Democratic convention. By August, the hackers had learned to use the language of Americans frustrated with Washington to create doubt about the integrity of the electoral system: "As you see the U. S. presidential elections are becoming a farce," they wrote from Russia.
仅这过去的六月,华盛顿邮报报道”俄罗斯政府黑客“黑进了美国民主党全国委员会(DNC)的服务器之中,俄罗斯的破坏活动立刻闯入公众视野之中。这些黑客有着一些不吉利的别名像是古琦费尔2.0(Guccifer2.0)和DC Leaks。在六月,他们宣称他们已经捕获到他们的第一个猎物,DNC主席黛比 沃瑟曼 舒尔茨(Dibbie Wasserman Schultz),在民主党全国代表大会召开之前几天他的私人邮件被维基解密公开。截至八月,黑客已学会使用美国人对华盛顿感到沮丧的语言来制造人们对选举系统整体性的怀疑。”“正如你们所见,美国总统选举证变为一场闹剧”他们从俄罗斯写道。
The attacks against political organizations and individuals absorbed much of the media's attention this year. But in many ways, the DNC hack was merely a prelude to what many security researchers see as a still more audacious feat: the hacking of America's most secretive intelligence agency, the NSA.
今年针对政治组织与个人的攻击吸引了媒体大量的关注。但从许多方面来看,许多安全研究专家认为,这次美国民主党全国委员会的黑客袭击事件仅仅是一场更加大胆的袭击行动的前奏,一场针对美国国家安全局(NSA)的黑客攻击。
Russian spies did not, of course, wait until the summer of 2015 to start hacking the United States. This past fall, in fact, marked the twentieth anniversary of the world's first major campaign of state-on-state digital espionage. In 1996, five years after the end of the USSR, the Pentagon began to detect high-volume network breaches from Russia. The campaign was an intelligence-gathering operation: Whenever the intruders from Moscow found their way into a U. S. government computer, they binged, stealing copies of every file they could.
俄罗斯间谍在2015年夏天便已经开始对美国展开黑客攻击。事实上,这个秋天正好是世界第一活动——国家间的网络间谍活动20周年。1996年,即苏联解体5年之后,美国五角大楼便探测到大量的来自俄罗斯的网络破坏活动。这些活动室情报收集行为:那些来自莫斯科的侵入者只要一黑进美国政府的电脑就毫无节制的偷窃他们能找到的每一份文件。
By 1998, when the FBI code-named the hacking campaign Moonlight Maze, the Russians were commandeering foreign computers and using them as staging hubs. At a time when a 56 kbps dial-up connection was more than sufficient to get the best of Pets.com and AltaVista, Russian operators extracted several gigabytes of data from a U. S. Navy computer in a single session. With the unwitting help of proxy machines—including a Navy supercomputer in Virginia Beach, a server at a London nonprofit, and a computer lab at a public library in Colorado—that accomplishment was repeated hundreds of times over. Eventually, the Russians stole the equivalent, as an Air Intelligence Agency estimate later had it, of "a stack of printed copier paper three times the height of the Washington Monument."
截至1998年,FBI给这些黑客活动以月光迷宫代号的时候,俄罗斯人正操控着国外的电脑并将这些电脑作为数据集结中心。每次当56kbps的拨号连接就能很好地访问Pets.com和AltaVista,俄罗斯黑客们在单个回话里从美国海军的计算机中提取到几个G的数据。在毫不知情的情况之下,美国弗吉尼亚的超级计算机,伦敦一家非盈利机构的服务器和科罗拉多公共图书馆的计算机实验室成为了帮凶,黑客们通过这些代理机器,一次又一次完成他们的黑客攻击任务。最终,根据空军情报局的估算,俄罗斯偷窃的文件如果打印堆起来又3倍华盛顿纪念碑的高度。
The Russians stole the equivalent of "a stack of printed copier paper three times the height of the Washington Monument."
俄罗斯偷窃的文件打印堆起来有3倍华盛顿纪念碑的高度
The Russians' tactics became more sophisticated over time; they even hacked satellites to cover their tracks. But while the American code names used to track the Russian effort changed—from Moonlight Maze to Storm Cloud to Makers Mark—the operation itself never really stopped. Over the next two decades, the FSB (successor to the KGB) and the GRU (Russia's premier military intelligence organization) went after political and military targets, while the NSA and the UK's GCHQ returned the favor.
随着时间的推移,俄罗斯的策略变得更加老练,他们甚至会攻击卫星以掩藏他们的踪迹。尽管美国给他们的活动代号从月光迷宫(Moonlight Maze)到风暴之云(Storm Cloud)再到制造商马克(Maker Mark),俄罗斯黑客的活动却从来就没有停止国。在这之后20年,俄罗斯联邦安全局(FSB)(前身位克格勃KGB)和格勒乌(苏军总参谋部情报局,俄罗斯最高情报组织)一直在追求他们的政治和军事目标,同时美国国安局和英国政府通讯总部对此也做出了回应
This sort of espionage was business as usual, a continuation of long-standing practice. And during the cold war, both the USSR and the United States subtly, and sometimes covertly, interfered with foreign elections. What changed over the past year, however—what made the DNC hack feel new and terrifying—was Russia's seeming determination to combine the two. For the first time, Russia used a hacking operation, one that collected and released massive quantities of stolen information, to meddle in an American presidential election. The inspiration and template for this new attack was a poisonous cocktail of fact and fabrication that the Russians call kompromat, for "compromising material."
这种间谍活动是正常的,这是长期活动的延续。在冷战期间,苏联和美国都曾巧妙地,有时隐秘地干预外国选举。然而过去一年发生了变化,这些变化使人对DNC的黑客攻击感觉新奇和可怕,俄罗斯似乎决心将这两者结合起来。这是第一次,俄罗斯执行黑客攻击收集和发布大量被窃信息来干涉美国总统选举。这次新的攻击的灵感和范本就像事实和谎言调配的鸡尾酒,俄罗斯人称之为Kompromat,即影响材料/污点材料。
Kompromat had been deployed by the Soviet Union since at least the 1950s, but in 1999 the Kremlin gave the tactic a high-tech update. With parliamentary elections fast approaching, and with post-USSR corruption at a peak, the government of president Boris Yeltsin used anonymous websites to sling mud at opposition candidates. One notorious kompromat repository was run specifically to slander the mayor of Moscow, a rising star in the opposition with his eyes on the presidency. In 2009, a senior British diplomat working in Russia was forced to resign after the appearance online of a four-minute video that showed him having sex with two blond women in a brothel.
影响/污点材料策略至少在上世纪50年代便已由苏联开始执行,但是在1999年克里姆林宫对这项策略进行了一次高技术升级。随着国家杜马选举的临近和后苏联腐败达到顶峰,政府总统鲍里斯 叶利钦通过一个匿名网站向反对派候选人泼脏水。一个臭名昭着的污点材料策略智囊团运作了明确针对莫斯科市长的中伤诽谤,这位市长是反对阵营的政治新星,他的目标直指总统宝座。在2009年,一位英国驻俄罗斯的高级外交官因为网上的一段4分钟视频而被迫辞职,在视频里该外交官在妓院与两名金发女人发生性关系。
One of the first American targets of kompromat was Victoria Nuland, who served as the top U. S. diplomat for Europe during Obama's second term. In February 2014, at the peak of the crisis in Ukraine, Nuland was surreptitiously recorded while speaking on the phone with the U. S. ambassador to Kiev. Frustrated with Europe's lackluster response to the Ukrainian crisis, Nuland said, "Fuck the EU." Shortly after, an aide to the Russian deputy prime minister tweeted a link to a recording of the intercepted phone call. The State Department called the leak "a new low in Russian tradecraft."
维多利亚 纽兰是污点材料策略第一批目标之一,在奥巴马的第二个任期里她是美国驻欧洲的最高外交官。在2014年2月,乌克兰危机处于紧急关头之时,纽兰在与美国驻乌克兰大使通话时遭到暗中录音,在电话中纽兰表达了对欧洲对乌克兰危机反应乏力的失望不满,纽兰说“OOXX欧盟”。没多久,俄罗斯副总理的一位助理便推送了一条链接,记录了截获的整通电话。美国国务院将这次泄密称之为应对俄罗斯间谍技术的新低点。
Victoria Nuland
The Nuland leak prompted a minor diplomatic hiccup between the European Union and the United States. But the kompromat campaign of the past year appears to be aimed at much bigger game: the American electoral system. According to Reuters, the FBI first contacted the DNC in the fall of 2015, obliquely warning the Democrats to examine their network. It wasn't until May, however, that the DNC asked for help from a cybersecurity company called CrowdStrike, which had experience identifying digital espionage operations by nation-states. CrowdStrike immediately discovered two sophisticated groups of spies that were stealing documents from the Democrats by the thousands.
纽兰泄密事件在美国和欧洲之间引起了一场小小的外交风波。但是在过去的一年污点材料活动明显指向了一个更大的目标:美国选举系统。根据路透社的消息,FBI曾在2015年秋天拐弯抹角地警告过民主党全国委员会DNC,让谈们检查他们的网络。可是直到五月份DNC才向一家名为CrowdStrike的互联网安全公司寻求帮助,这家公司在鉴别由国家政府发动的网络间谍活动和怒有经验。CrowdStrike立即就发现有两个老练的间谍集团正在偷窃民主党数千份文件。
CrowdStrike was soon able to reconstruct the hacks and identify the hackers. One of the groups, known to the firm as Cozy Bear, had been rummaging around the DNC since the previous summer. The other, known as Fancy Bear, had broken in not long before Putin's appearance at the St. Petersburg forum. Surprisingly, given that security researchers had long suspected that both groups were directed by the Russian government, each of the attackers seemed unaware of what the other was doing.
CrowdStrike很快就重构的这次黑客攻击,鉴别出黑客身份。其中一个团体,以一家名为舒适熊Cozy Bear的团伙,这个团体自去年夏天就一直在DNC周围导出搜寻。另一个团体以幻想熊Fancy Bear为名字,不久之前海出现在圣彼得堡的普京聚会上露过面。令人惊讶的是,安全研究专家长期怀疑这两个团体都是有俄罗斯政府领导,但是这两个团体好像并不知道互相正在做些什么。
Meanwhile a mysterious website named DC Leaks was registered on April 19. In early June, a Twitter account associated with the site started linking to the private conversations of Philip Breedlove, who had been, until a few weeks earlier, NATO's Supreme Allied Commander in Europe. DC Leaks was well designed, but nobody seems to have noticed it until early July.
其间一个名为DC Leaks的网站在4月19日注册了。在六月初,一个和这个网站相关的推特账号开始连接北约欧洲盟军司令菲利普 布里德洛夫的会话。DC Leaks这个网站设计的很好,但是在7月初之前似乎没有人注意到这个网站。
DC Leaks was well designed, but nobody seems to have noticed it until early July.
DC Leaks这个网站设计的很好,但是在7月初之前似乎没有人注意到这个网站
On June 14, less than an hour after The Washington Post reported the breach at the DNC, CrowdStrike posted a report that detailed the methods used by the intruders. The firm also did something unusual: It named the Russian spy agencies it believed responsible for the hack. Fancy Bear, the firm said, worked in a way that suggested affiliation with the GRU. Cozy Bear was linked to the FSB.
在6月14日,华盛顿邮报报道对DNC的入侵事件不到一小时,CrowdStrike就发布了一份报告,报告详述了侵入者使用的方法。该入侵团伙也做了一些不同寻常的事:它宣称俄罗斯情报机构为此负责。Fancy Bear这个团伙说他们的工作方式与格勒乌GRU相关,而Cozy Bear则是与俄罗斯联安全局FSB有联系。
The day after the Post story broke, a website appeared that claimed to belong to a hacker who identified himself as Guccifer 2.0. (Guccifer was the nickname of a Romanian hacker who, among other things, broke into the email account of George W. Bush's sister.) The operators, posing as Guccifer 2.0, dismissed CrowdStrike's attribution, insisting instead that the DNC had been "hacked by a lone hacker." As proof, Guccifer published eleven documents from the DNC, including an opposition-research file on Donald Trump and a list of major Democratic donors. In the weeks that followed, Guccifer offered interviews and batches of documents to several journalists, but he wrote that "the main part of the papers, thousands of files and mails, I gave to WikiLeaks."
在华盛顿邮报报道这个事件的前一天,一个网站现身并且宣称他就是这次事件的袭击者,他称呼自己为Guccifer2.0(Guccifer是一个罗纳尼亚黑客的绰号,他在其它的事件中,攻破了乔治 W 布什的妹妹多萝西·布什·科克的电子邮件账户)。这名操作者把自己装扮成Guccifer,毫不理会CrowdStrike的调查结果,坚称DNC仅仅是被一单独的黑客袭击。为了证明这一点,他公布了从DNC偷窃而来的文档资料,其中包括对竞争对手唐纳德 特朗普的研究,还有一个民主党主要捐献者的名单。在接下来的几个星期,Guccifer接受了记者的采访,并且把一批文档资料交给了几名记者,但是他表示这次偷窃而来的资料的最重要的部分——几千份文件和电子邮件,他将交给维基解密WikiLeaks。
Ultimately, more than two thousand confidential files from the DNC found their way to the public. Throughout the campaign, Guccifer maintained that he was the only person behind the hacking and leaking. "This is my personal project and I'm proud of it," he—or they—wrote in late June. But several sloppy mistakes soon revealed who was really behind the operation. The unraveling happened more quickly than anybody could have anticipated.
最终来自DNC的几千份机密文件向公众公布了。在整个事件当中,Guccifer都坚持宣称整个黑客攻击与泄密事件的幕后之人就只有自己。“这是我个人的项目,我为此感到骄傲”,在六月下旬他或者他们这样写道。然而不久几个粗心的错误透露出到底是谁在背后操作整个事件。整个事件的秘密比任何人能想到的更快地揭开了。
As soon as Guccifer's files hit the open Internet, an army of investigators—including old-school hackers, former spooks, security consultants, and journalists—descended on the hastily leaked data. Informal, self-organized groups of sleuths discussed their discoveries over encrypted messaging apps such as Signal. Many of the self-appointed analysts had never met in person, and sometimes they didn't know one another's real names, but they were united in their curiosity and outrage. The result was an unprecedented open-source counterintelligence operation: Never in history was intelligence analysis done so fast, so publicly, and by so many.
在Guccifer的公布的文件在互联网炸开锅后不久,一大群调查者快速奔向了泄露的数据,这其中包括老牌黑客,前间谍人员,安全顾问和记者。一些非正式的自发侦查组织讨论了他们有关加密通讯应用比如Signal的一些发现。许多自封的分析专家从来就没有碰过面,他们甚至不知道对方的名字,但是他们在自身的好奇心和愤怒之下联合起来。结果就是一个开源的反情报行动以前所未有之情形组织起来了:历史上从未有情报分析向这样快速,公开,由如此多的人完成。
Matt Tait, a former GCHQ operator who tweets from the handle @pwnallthethings, was particularly prolific. Hours after the first Guccifer 2.0 dump, on the evening of June 15, Tait found something curious. One of the first leaked files had been modified on a computer using Russian-language settings by a user named "Feliks Dzerzhinsky." Dzerzhinsky was the founder of the Cheka, the Soviet secret police—a figure whose mythic renown was signaled by a fifteen-ton bronze statue that once stood in front of KGB headquarters. Tait tweeted an image of the document's metadata settings, which, he suggested, revealed a failure of operational security.
Matt Tait是一个前英国政府政府通讯总部GCHQ人员,从“the hanle @pwnallthethings”发送推文,披露了大量的研究结果。在Guccifer公开第一批数据仅仅几小时后,即在6月15日夜间,Tait发现了一些有趣的东西。在第一批文件中有一份文件在一台使用俄罗斯语言的用户名为Feliks Dzerzhinsky的电脑上修改过。捷尔任斯基是契卡(全俄肃反委员会)创始人,苏联秘密警察,看到这儿名字,脑海中就会浮现一幅图像,一座15吨重的青铜雕像矗立在克格勃总部大楼之前,并由此联想到捷尔任斯基那神话般巨大的声望。Tait推送了文件元数的图像。图像现实出安全操作的失败。
A second mistake had to do with the computer that had been used to control the hacking operation. Researchers found that the malicious software, or malware, used to break into the DNC was controlled by a machine that had been involved in a 2015 hack of the German parliament. German intelligence later traced the Bundestag breach to the Russian GRU, aka Fancy Bear.
第二个错误与被用来控制黑客操作的计算机有关。研究者发现那些用来突破防护的恶意软件被一台机器所控制,而这台机器又和2015年德国议会的黑客事件有关。德国情报机构追查德国国家议会黑客事件,线索最后直指俄罗斯格勒乌,亦称Fancey Bear。
There were other errors, too, including a Russian smile emoji—")))"—and emails to journalists that explicitly associated Guccifer 2.0 with DC Leaks, as the cybersecurity firm ThreatConnect pointed out. But the hackers' gravest mistake involved the emails they'd used to initiate their attack. As part of a so-called spear-phishing campaign, Fancy Bear had emailed thousands of targets around the world. The emails were designed to trick their victims into clicking a link that would install malware or send them to a fake but familiar-looking login site to harvest their passwords. The malicious links were hidden behind short URLs of the sort often used on Twitter.
这里也有其它的错误,互联网安全公司指出,这其中就包含有一个俄罗斯微笑表情“)))”,还有那些给记者的邮件也明确地表明了Guccifer和DC Leaks有着某种联系。但是黑客们一个严重的错误就发生在他们用来发动攻击的邮件上。这只是称之为鱼叉式网络钓鱼的活动的一部分。Fancy Bear向全世界几千个目标发送了邮件,这些邮件都被设计好了,他们会欺骗受害者去点击一个链接,这个链接要么会诱发安装恶意软件,要么会将受害者引向一个看起来很相似但其实却是虚假的网站,一旦登陆账户,密码便会被盗窃。
To manage so many short URLs, Fancy Bear had created an automated system that used a popular link-shortening service called Bitly. The spear-phishing emails worked well—one in seven victims revealed their passwords—but the hackers forgot to set two of their Bitly accounts to "private." As a result, a cybersecurity company called SecureWorks was able to glean information about Fancy Bear's targets. Between October 2015 and May 2016, the hacking group used nine thousand links to attack about four thousand Gmail accounts, including targets in Ukraine, the Baltics, the United States, China, and Iran. Fancy Bear tried to gain access to defense ministries, embassies, and military attachés. The largest group of targets, some 40 percent, were current and former military personnel. Among the group's recent breaches were the German parliament, the Italian military, the Saudi foreign ministry, the email accounts of Philip Breedlove, Colin Powell, and John Podesta—Hillary Clinton's campaign chairman—and, of course, the DNC.
为了管理如此多的短链,Fancy Bear创建了一个自动服务系统,这个系统使用了非常受欢迎的短链服务Bitly(bit.ly)。鱼叉式网络钓鱼攻击效果良好,每7个人就有一个暴露了密码,但是何可们却忘记了将其中两个Bitly账户设置为私密。结果,一个名为SecureWorks的互联网安全公司查到Fancy Bear攻击目标的信息。在2015年10月到2016年5月,期间,黑客团伙使用了9000个链接攻击了大约4000个谷歌账户,这些目标包括乌克兰,波罗的海国家,美国,中国,伊朗。Fancy Bear试图增加对国防部长,驻外大使,驻外武官这类人员的攻击。受攻击最多的多是现任和前任军事人员,大约占整个攻击活动的40%。这些团伙的成果包括对德国国家议会,意大利军方,沙特外交部的渗透,以及对菲利普 布里德洛夫,科林 鲍威尔以及约翰 波德斯塔——希拉里 克林顿竞选总干事当然还有民主党全国委员会的电子邮件账户窃取。
The rapid public reconstruction of the DNC break-in appears to have caught the hackers off guard. Researchers surmised that the Russian spies had not expected to be identified so quickly, a theory that would explain, among other things, the peculiar animus Guccifer seemed to have for CrowdStrike. According to this hypothesis, the tradecraft blunders that Tait and others had identified were the result of a hasty effort by the GRU to cover its tracks.
公众对于整个DNC侵入事件重构是如此地迅速以至于让那些黑客措手不及。研究者推测估计怎么也没有料到鉴别工作进行得如此快速,他们也没有准备一些说辞来解释整个事件中Guccifer对CrowdStrike异乎寻常的敌意。根据这些推测,Tait和其他的人发现的那些因为间谍技术留下的错漏之处应该是GRU急于掩藏自身踪迹而留下的。
As if to regroup after the initial rush of activity, Guccifer and DC Leaks went quiet at the end of June. But the 2016 presidential campaign, already the most bizarre in living memory, had a further surprise in store, one that worked in favor of the Russians. At a time when only 32 percent of Americans say that they trust the media to report the news fairly and accurately, the hackers were about to learn that getting called out publicly didn't really matter: Their kompromat operations would still work just fine.
在最初的快速紧张行动之后,Guccifer和DC Leaks在六月底一起沉寂下去了,但这次似乎他们又一次集结,在2016年的美国总统选举在人们的心中也成为一场闹剧,在这场闹剧中还有这令人震惊的事情即将发生,这些事情对于俄罗斯确实利好的。在这个仅有32%的民众相信媒体能够客观公正报道新闻的情况之下,黑客们了解到公开号召公众已经不要紧了。他们的污点材料策略仍然有很好的效果。
The hackers were about to learn that getting called out publicly didn't really matter.
黑客们了解到公开号召公众已经不要紧了
On July 22, three days before the Democratic National Convention in Philadelphia, WikiLeaks published the largest trove of files to date, which included nearly twenty thousand hacked emails. Press coverage of the release quickly centered on emails that suggested a bias among some DNC staffers in favor of Hillary Clinton. The leaked emails lent credence to a suspicion held by some Democrats that the party establishment had never intended to give Bernie Sanders, Clinton's opponent in the primaries, a fair shake. Protesters in Philadelphia held up signs that read election fraud and dnc leaks shame. One day before the convention, the Russian kompromat campaign took its first trophy: Debbie Wasserman Schultz, the DNC chair, resigned from the organization.
在费城举行的民主党全国代表大会之前的三天,即6月22日,维基解密公布了迄今为止最多的泄密文件,包括20000份电子邮件。新闻报道快速集中到这些电子邮件的内容上,这些邮件显示一些民主党全国委员会DNC的一些成员偏袒支持希拉里 克林顿。这些泄密的邮件证实了一些民主党人的怀疑——在初选中,党内当权者就从来没有打算给克林顿的对手伯尼 桑德斯公平的待遇。费城的抗议者举着牌子抗议,牌子上写着选举欺骗和DNC泄密丑闻。在大会前一天,俄罗斯的污点材料策略赢得了他们的第一个战利品:黛比 沃瑟曼 舒尔茨,DNC主席,从委员会辞职。
The episode shocked the Democratic establishment, not least because of what it augured for the future. As Clinton's lead in the polls widened after the convention, commentators began to speculate that a damaging leak late in the campaign might be the only chance for Donald Trump to win the election. Fears of a Russia-sponsored October surprise grew as it became clearer that the subversion effort was improving. When files appeared, they were now scrubbed of the sort of distinguishing metadata that had allowed analysts to trace the leak back to Russian intelligence.
这一事件震惊了整个民主党,尤其是因为这件事对今后情况的影响。在民主党大会之后,克林顿的领先地位扩大了。评论员开始推测在选举的最后关头一次又破坏性的泄密可能是唐纳德 特朗普赢得本次选举的唯一机会。随着颠覆活动逐渐起到越来越好的效果,对于俄罗斯赞助支持的十月惊奇的害怕情绪也在与日俱增。现在披露的文件已经被擦去了那些能引导分析者将泄密事件指向俄罗斯的显眼元数据。
The operators behind Guccifer and DC Leaks also appear to have recognized that American journalists were desperate for scoops, no matter their source. The Russians began to act like a PR agency, providing access to reporters at Politico, The Intercept, and BuzzFeed. Journalists were eager to help. On August 27, when part of the DC Leaks website was down for some reason, Twitter suspended the @DCLeaks account. The Daily Caller, a conservative news website, posted a story about the events, drawing an outcry from Trump supporters. Lou Dobbs, the Fox Business anchor, sneered that "leftist fascism" was throttling the last best hope for a Trump victory. Twitter soon reinstated @DCLeaks.
Guccifer和DCLeaks背后的操纵者也似乎意识到美国的新闻记者也很渴求着先度假爆料,根本不在乎这些新闻的来源就想搞个大新闻。俄罗斯人开始像一个公关公司一样行动,为Politico(PolitiCo:美国政治新闻网,是美国的一个政治新闻组织创办的媒体新闻网站)的记者提供采访机会。The Intercept(The Intercept:美国调查新闻网站)和BuzzFeed(BuzzFeed:美国新闻聚合网站)的记者也迫切需要这种帮助。在8月27日,由于某些原因DC Leaks网站的部分资料下线了。推特禁了@DCLeaks的账号。每日传讯(Daliy Caller:一家总部设在花神棍的新闻与舆论网站),一个保守新闻网站,发布了整个事件的新闻报道,引来了特朗普支持者的强烈抗议。福克斯商业网(FoxBusiness:一个美国有线新闻和卫星新闻电视商业网,福克斯娱乐集团旗下商业网络之一,福克斯娱乐集团属于默多克新闻集团)新闻栏目主播卢 多布斯嘲笑说左派法西斯主义扼杀了特朗普赢得选举胜利的最后希望。推特不久就恢复了@DCLeaks的账号。
The most effective outlet by far, however, was WikiLeaks. Russian intelligence likely began feeding hacked documents to Julian Assange's "whistleblower" site in June 2015, after breaching Saudi Arabia's foreign ministry. A group called WikiSaudiLeaks, probably a Guccifer-like front for Fancy Bear, claimed that "WikiLeaks have been given access to some part of these documents." The so-called Saudi Cables showed princes buying influence and monitoring dissidents. They became a major news story, proving that the old methods worked even better in the twenty-first century.
然而到目前位置最有效的泄密渠道仍然是维基解密,在侵入沙特外交部之后,2015年6月俄罗斯的情报机构可能开始向阿桑奇的网站“举报人”提供这些黑来的文件。一个名为维基沙特解密可能是类似于Guccifer这样的为Fancy Bear打掩护的团伙宣称“维基解密已经被授权访问事关沙特泄密的部分文档。那份称为沙特电报(The Saudi Cable)的文件显示沙特王子购买影响力和监控不同政见者。这些事件都成为媒体的主要新闻报道,同时证明了老方法在21世纪甚至更加有效。
Julian Assange
A leak released at the end of this past summer showed how frictionlessly the kompromat campaign was able to operate in the fact-free atmosphere of the 2016 American presidential campaign. In late September, DC Leaks published hundreds of emails from the account of a twenty-two-year-old freelancer for the Clinton campaign. Lachlan Markay, a reporter for The Washington Free Beacon, found an audio clip buried deep in the cache. In the recording, which was made at a fundraiser in Virginia, Hillary Clinton could be heard describing Sanders supporters as "children of the Great Recession" who "are living in their parents' basement." The comments were clumsy but, in context, hardly damning; Clinton was describing the appeal of Sanders's "political revolution" for young voters. ("We want people to be idealistic," she said.) Nevertheless, within a few days, Donald Trump was telling a roaring crowd in Pennsylvania, "Clinton thinks Bernie supporters are hopeless and ignorant basement dwellers."
在这个夏天即将过去的时候,一份泄密文件揭露了在2016年这个充满欺骗与谎言的总统竞选当中俄罗斯的污点材料策略是如何毫无障碍地运作下去的。在9月下旬,DC Leaks公布了一个为克林顿竞选活动工作的自由职业者的几百份电子邮件。华盛顿自由灯塔报(Washington Free Beacon:美国一家倾向保守党派的政治新闻网站)的一个名为拉克兰 马凯(Lachlan Markay)的记者在缓存文件中找到了一份音品片段。这段录音是在弗吉尼亚的一个资金筹集活动上录制的,在录音里希拉里 克林顿把桑德斯的支持者称之为生活在他们父母的地下室的大萧条的孩子。这个评论有些不得当,但是在当时的情景之下,这些话也算不得是咒骂。克林顿海描叙桑德斯的”政治革命“对年轻人的吸引力。(我们想每个人都成为理想主义者,克林顿说)。然而,几天之后,特朗普就在宾夕法尼亚州向呼号的人群说“克林顿认为桑德斯的支持者都是不可救药和愚蠢无知的地下室居住者”
In mid-August, when Guccifer and DC Leaks were making near-daily news, a third mysterious social-media account popped up out of nowhere. A group calling itself the Shadow Brokers announced that it had published "cyberweapons" that belonged to the NSA on file-sharing sites such as Github. The group said that it would soon hold an auction to sell off a second cache of tools. After a security researcher posted a link to a repository of the supposed NSA software, analysts flocked to the dump. Security researchers quickly discovered that the tools, a collection of malware designed to steal data from their targets, were the real thing. Crucially, The Intercept, a media outlet with access to the NSA files leaked by Edward Snowden, found a sixteen-character string ("ace02468bdf13579") in the Shadow Brokers' tools that was referenced in a top-secret, and previously unpublished, NSA manual. The connection proved the provenance of the Shadow Brokers' find.
在8月中旬,当Guccifer和DC Leaks几乎每天都在搞大新闻的时候,一个第三方的社交媒体账号不知从什么地方冒出来,这个团伙自称影子代理人(Shadow Bokers),他们在诸如Github这样的文件分享网站上发布了一个属于美国国家安全局NSA的网络武器。这个团伙还说不就之后他们他们还会举行一个拍卖出售第二个工具。在一个研究者发布了一个指向据说是NSA软件位置的链接,大批分析者蜂拥而至下载软件。安全研究专家很快发现这些用于偷窃目标数据的软件工具合集都是真的。关键的是,The Intercept这家能够接触到爱德华 斯诺登(Edward Snowden)的媒体在Shadow Bokers的工具总发现了一个16位字符的字符串,而这个字符串在一个绝密以前从未公开的手册里出现过。这个联系证明了Shadow Bokers所说的话的真实性。
Robbing the NSA, of course, is not easy. The agency's elite hacking unit, called Tailored Access Operations, has an internal network known as the "high side" that is physically segregated from the Internet (the "low side"). Data diodes, devices that allow data to flow one way only, like water from a faucet, make it nearly impossible to hack high-side computers from the low side. When TAO hackers want to attack an adversary, they move their tools from the high side to a server on the low side, navigate through a series of addresses that make their tracks difficult to trace, and install malware on their target. To steal the NSA's malware, the Shadow Brokers had to compromise a low-side machine that the TAO was using to hack its targets. The Shadow Brokers likely got lucky: Some analysts believe that an NSA operator mistakenly uploaded a whole set of tools to a staging computer the hackers were already watching. The alternative theory: an old-fashioned mole passed on the tools.
偷到NSA的东西可不容易。美国国家安全局的优秀的黑客攻击单元称为定向访问攻击,这种攻击模式下,有一个与互联网(低侧)物理隔绝的内网(高侧)。数据二极管是一种只允许数据单向流动的设备,这就像水只能从单向从水龙头流出一样,这样基本上不可能从低侧向高侧发起网络攻击。当执行定向访问操作的黑客们向攻击一目标时,他们会将他们的工具从高侧转移到一个低侧服务器上面,通过一系列难以追查踪迹的地址来使用工具对他们的目标进行操纵和安装恶意软件。为了偷到这些软件,Shadow Bokers不得不让出一台低侧服务器让他们用来进行定向访问操作。Shadow Bokers可能是走了个狗屎运:一些分析家认为,某个NSA操作员错误的上传了整套工具集到分级电脑上,而这台电脑正被人监控,这种情况可能的解释就是:一个守旧保守的间谍在传递这套工具。
After going to all that trouble, why publish the results? A possible answer is suggested by a surprising discovery made by the U. S. intelligence community around the time Putin was addressing the journalists in St. Petersburg. American investigators had long known that the Russians were doing more than spear-phishing, but sometime around April they learned that the intruders were using commercial cloud services to "exfiltrate" data out of American corporations and political targets. Cozy Bear, the hacking group believed to be affiliated with the FSB, used some two hundred Microsoft OneDrive accounts to send data from its victims back to Moscow.
转回到所有的这些麻烦事,为什么公布结果?一个可能的答案就是,大约普京在圣彼得堡向记者们发表自己的演说的时候,美国情报界发现了一些惊人的东西。美国调查人员一直都知道俄罗斯不仅仅只是在做鱼叉式网络钓鱼,大约在4月的某个时候,他们了解到侵入者正在使用商业云服务来将美国公司和政治目标的数据偷偷地转移出去。Cozy Bear这个黑客团伙据信隶属于FSB,他们使用两百个微软的OneDrive账户将那些受害者的数据传回莫斯科。
Using cloud services such as OneDrive was a clever but risky move—it was a little like taking the bus to make off with stolen goods from a burglary. Though the widespread use of the services by legitimate users offered a degree of cover for the hackers, data provided by Microsoft also helped America's elite digital spies identify the DNC intruders "with confidence" as Russian. It is even possible that the U. S. government has been able to identify the names and personal details of individual operators. The Russians knew they'd been caught. On July 30, an FSB press release announced that twenty government and defense organizations had been hit by high-powered spying tools.
使用诸如OneDrive这样云服务虽说是个聪明的做法,但同时这也是有风险的,这有点像小偷搭乘公共汽车卷赃潜逃。虽然大规模使用合法用户服务来转移数据的这种方法为黑客提供了某种程度上的掩护,但是美国的网络间谍的精英们通过分析微软提供的数据很确信袭击DNC的那些黑客就是俄罗斯的。甚至有可能,美国政府已经能够侦查出那些黑客们的名字和个人的详细信息。
Some intelligence analysts believe that the Shadow Brokers' publication of the NSA spy kit was a message from one group of professionals to another. "You see us?" the Russians seemed to be saying, perhaps in reference to ongoing U. S. efforts to investigate the DNC breach. "Fine, but we see you, too." Similarly, the announcement of an auction—all but certainly phony—was probably intended as a warning that the hackers were prepared to publish a key that would unlock an encrypted container holding a second batch of stolen tools. Like a severed ear in an envelope, the announcement told the Americans: Don't mess with us.
一些情报分析家认为,Shadow Bokers公布NSA的间谍工具套装是一个专业团体向另一个专业团体传达某种信息。俄罗斯人似乎再说"嘿,你们看到我们没?",这可能和美国对于DNC泄密事件调查进度的不断向前推进有关。“好吧,但现在我们也看到你了。”与此类似,那个几乎可以确定为是假的拍卖声明也很可能是一个警告,黑客们已准备好发布一个能够解锁解密了第二批工具的容器的密钥。就像信封里的一个断耳,这份声明告诉美国人:不要糊弄我们。
Like a severed ear in an envelope, the announcement told the Americans: Don't mess with us.
就像信封里的一个断耳,这份声明告诉美国人:不要糊弄我们
Meanwhile, the kompromat campaign proceeded apace. August and September each saw six data dumps, including files from the Democratic Congressional Campaign Committee, which had also been hacked. In October, as the presidential election drew near, Guccifer published a massive cache, more than twenty-one hundred files. Three days later, WikiLeaks began publishing thousands of emails stolen from John Podesta's account.
与此同时,污点材料策略活动在快速地向前推进。8月和9月这两个月都能见到6次大规模数据流,包括民主党国会竞选委员会也被黑客攻击了。在10月,总统选举临近,Guccifer发布了大量文件,数量超过2100份。3天后维基解密开始发布约翰 波德斯塔(希拉里竞选总干事)的几千份电子邮件。
On the day WikiLeaks published the first batch of Podesta's emails, the U. S. government took the unprecedented step of announcing that it was "confident" Russia's "seniormost officials" had authorized the DNC hacks. So far U. S. investigators have not said publicly who was responsible for the Podesta hack, but the data harvested by SecureWorks makes it clear that Fancy Bear broke into the Clinton chairman's account as early as late March. The CIA briefed Trump about the origin of the kompromat, but he continued to cite the material, telling a Pennsylvania crowd, "I love WikiLeaks!"
在维基解密发布一系列波德斯塔的邮件的时候,美国政府采取了空前的举动,宣称他们确信是俄罗斯的最高官员授权了此次对DNC黑客攻击。到目前为止,美国的调查员还没有向公众说明到底谁应该为对波德斯塔的黑客攻击负责,但是根据SecureWorks掌握的数据来看,有一点是可以确定的,早就在5月下旬,克林顿竞选总干事的账户便已经被黑客攻破。中央情报局(CIA)向特朗普简要说明了污点材料策略的来源(希望特朗普顾及美国利益不要以此为噱头),但是特朗普还是继续引用这些材料,并且告诉宾夕法尼亚的民众“我爱维基解密!”
On October 12, Putin appeared at another forum, this time with more than five hundred guests in Moscow. Sitting comfortably in front of a giant banner that said russia calling! he answered an audience question about the hacks. "Everyone is talking about who did it," Putin said. "Is it so important?" The former KGB officer, proving his full command of U. S. political intrigue, suggested that the Democrats had "supported one intraparty candidate at the expense of the other." Any talk of the hacks being in Russia's interest, he said, was "hysteria" intended to distract Americans from what the hackers discovered: "the manipulation of public opinion." When the audience applauded, a smirk returned to Putin's face. "I think I answered your question," he said.
在10月12日,普京出现在另一个莫斯科的论坛(俄罗斯外贸银行“俄罗斯在召唤”投资论坛)上,这次又超过500名观众。普京舒坦地坐在巨大的横幅之前,横幅上写着“俄罗斯在召唤”。他回答了有关黑客事件的问题,“每个人都在谈论到底是谁做了这些事”普京说“这重要?”这位前克格勃官员,向人们证明了他对美国政治阴谋的全盘掌握,并认为民主党是以牺牲另一个人为代价来支持一个(钦定)的党内候选人。“任何说黑客袭击有利于俄罗斯的言论都是”歇斯底里“,无稽之谈,这些指责只是为了分散美国公众注意力,是人们不在关注黑客发布的实质内容:对公众舆论的操纵。”当观众为此鼓掌之时,普京的脸上有露出迷之微笑,说“我认为我已经回答了你们的问题。”
版权声明
我们致力于传递世界各地老百姓最真实、最直接、最详尽的对中国的看法
【版权与免责声明】如发现内容存在版权问题,烦请提供相关信息发邮件,
我们将及时沟通与处理。本站内容除非来源注明五毛网,否则均为网友转载,涉及言论、版权与本站无关。
本文仅代表作者观点,不代表本站立场。
本文来自网络,如有侵权及时联系本网站。
图文文章RECOMMEND
热门文章HOT NEWS
-
1
Why do most people who have a positive view of China have been to ...
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
推荐文章HOT NEWS
-
1
Why do most people who have a positive view of China have been to ...
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10